Do you know what a Business Email Compromise scam is? Are you looking for tips to help protect your business from these types of scams? If so, read on. We will give you an overview of what email compromise scams are, how to find them, and how to protect your business from them.
Introduction to Business Email Compromise Scams
Business Email Compromise (BEC) scams are sophisticated attacks that target both businesses and individuals with the intention of stealing funds through ACH and wire transfer payments, and more recently Cryptocurrency. Here we will explain how BEC scams work, and the various types of threats associated with them.
BEC scams are financially motivated attacks that target businesses that use wire transfers and have suppliers abroad, and sometimes with domestic operations only. Scammers research their targets and figure out how to assume the identity of a C-Level executive or accounting manager to appear legitimate. They use social engineering tactics to make requests for wire transfers to be sent to a bank account controlled by the scammers, often with an unknowing money mule acting as an intermediary for better obfuscation through money laundering. These requests almost always appear to come from someone in a position of authority, such as a company executive or trusted vendor.
It is important to be aware of the various types of BEC threats in order to stay protected. These threats can include phishing emails, account takeover attacks, malware infections, business email spoofing, and domain spoofing. Additionally, attackers may use social media accounts or even impersonate a legitimate customer or vendor in order to make their requests seem more believable.
Learn more about the common types of Business Email Compromise scams.
Ironically, the Rexxfield team uses the same methods described above, to unmask the criminals, and in some cases even counter-scam them to help with client recoveries. But, everything we do is legal, admissible, and very compelling in court.
It is important for businesses to take proactive steps to protect themselves and their employees from falling victim to these types of scams. By taking the time to understand the risks associated with Business Email Compromise Scams, companies can ensure they are taking measures to protect themselves from these threats.
Steps to Spot a Business Email Compromise Scams
Business Email Compromise scams are becoming increasingly common. To protect yourself from becoming a victim of a BEC scam, you need to know how to spot the signs of a BEC scam. Here are some steps that can help you identify and investigate BEC scams:
1. Pay attention to email addresses, URLs, and spelling. Scammers often use fake email addresses and URLs that are similar to legitimate ones in order to gain your trust. Be sure to check for misspellings or other irregularities that could indicate the presence of a scammer.
2. Research the payment requester. Scammers often research their targets in order to gain insight into their behavior. It is important to do your own research before engaging with any suspicious emails or requests.
3. Listen to your gut. If something doesn’t look or feel right, don’t be afraid to investigate further before taking any action.
4. Contact your financial institution. If you suspect you have been targeted by a BEC scam, it is important to contact your financial institution immediately. This is in order to add an extra layer of protection from any potential losses.
5. File a complaint with the FBI. The FBI has created an online system for reporting cybercrime incidents such as BEC scams. If you believe you have been targeted by a BEC scam, filing a complaint can help law enforcement investigate and take action against the perpetrators.
6. Conduct a private digital investigation.
Once you have identified and reported the potential BEC scam, it is important to conduct an investigation in order to uncover and preserve any evidence related to the attack and identify potential perpetrators. Ideally, confirmation of the attack will be carried out by an experienced IT professional within your organisation. Then, the insights found should be passed on to a Business Email Compromise private investigator so that your investigation can be fast tracked and coordinated with law enforcement if necessary.
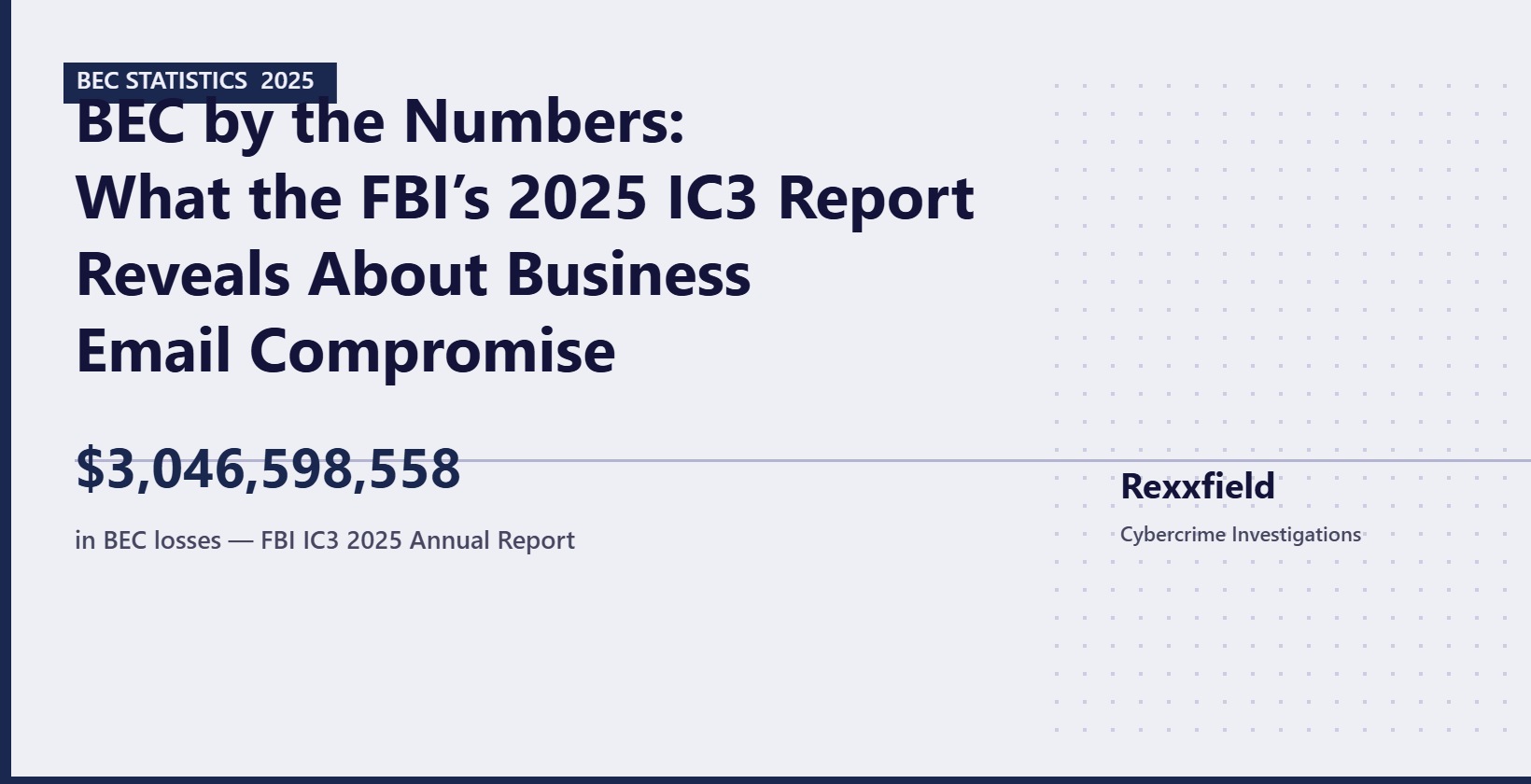
Did you know that there were 21,489 instances of BEC reported to the FBI’s IC3 in 2023, a considerable increase from 19,954 reports of BEC in 2021. Law enforcement simply does not have the resources needed to investigate and resolve this fast growing, lucrative cybercrime.
The IC3’s Recovery Asset Team (RAT) recovered less than 14% of reported BEC losses in 2021, and that’s without considering instances of BEC that weren’t reported.
Whereas, more than 90% of cybercrimes that Rexxfield investigates and refers to law enforcement have all the evidence needed for a successful outcome, greatly increasing the likelihood your case is accepted and justice is served.
Like us, your Cybercrime private investigators may be able to counter-engage the scammers in ways that get them to slip up and reveal their identities.
Follow the money! BEC scammers will often attempt to launder their scammed cash through the blockchain. Make sure your investigators also have qualified blockchain scam investigators.
By following these steps, you can protect yourself from becoming a victim of Business Email Compromise scams and take proper action if you suspect one is targeting your business or organization.
Investigate & Analyze Evidence
First, find and analyze the phishing email received from the spoofed email address. Look for differences between the email address, URL, and spelling as scammers often apply small variations so you don’t notice something is wrong, and gain your trust. Then look for the “source email” or “display original” options for the phishing email, to find the metadata. This can provide you with important evidence. Also, check when the email domain name was registered. If this was in the last day or weeks, that is a clear sign of a scam.
 THREAT MITIGATION:
THREAT MITIGATION:
Businesses can also simulate phishing emails to test and teach employees what they look like, and what to look for. This will help train employees to identify fraudulent emails and prevent attacks. Additionally, it’s important to add layers of protection, two-factor authentication or threat intelligence filters, to prevent BEC scams from happening.
By investigating suspicious emails received and educating employees, businesses can reduce their risk of falling victim to BEC scams and protect themselves from reputation damage, or financial losses.
Research the Attacker
As attackers do their research on business to gain trust and customize their attacks, you have to research the attacker. Start by gathering as much information as you can about the person or network behind the email.
Look for available public information like news articles, press releases, social media, and more, to determine if the sender is a legitimate business. Search Google for the domain name, email address, bank details, etc.
Contact Your Financial Institution Immediately
When you or your business is a victim of a BEC scam, the first thing you should do is contact your financial institution immediately. This will help to prevent any further fraud attempts and protect your money.
When you contact your financial institution, provide them with as much information as possible. This will help the financial institution to trace the fraudulent transaction and find out who is responsible. Also provide them with the phishing email(s) and bank statements. Also, make sure to have details to verify yourself as the owner of the account so the bank can act on your behalf.
Then you may want to consider engaging a civil lawyer to make sure that all legal implications are taken into account. Lawyers can offer advice on the next steps to try to recover lost funds and help with communication with your financial institution if needed.
File a Complaint with the FBI
Once you have identified and investigated a business email compromise scam, you need to file a complaint with the FBI. This will help provide law enforcement with the information they need to investigate the scam thoroughly, and you can help protect yourself and others from becoming victims of business email compromise scams.
You can file a complaint through the Internet Crime Complaint Center (IC3). Give the FBI as much information as possible: names, dates, email addresses, source code, and copies of the communication from the scammer, such as the email and other documents related to the BEC scam.
When submitting your complaint, include what you have done to identify the email and the information you found from doing your own investigation.
The information you submit to the FBI will be kept confidential. They will not share it with anyone outside of law enforcement.
Unfortunately…
IC3 Reporting Fact: Less than one in ten-thousand cybercrimes are prosecuted in the USA and other Western countries, so don’t get your hopes up for easy or fast justice.
Step-by-Step Guide for Digital BEC Investigation
Conducting a digital investigation helps to identify the source of the attack and provides insight into how it was done. Follow this step-by-step guide to cover everything:
Step 1: Analyze Email Headers.
Start with locating and analyzing the email headers. Open the phishing email, and go to “show original” or “view source”. This will open a new window with the metadata of the email. Look for any discrepancies between what is listed in the header and the legitimate emails. You may find things like an IP address, which will give you insight into the location of the criminals.
Step 2: Examine Network Traffic.
Examine your network traffic to find anything associated with the email attack. Analyze web requests or responses based on the time stamp and IP address to find any relevant network related to the malicious email. Furthermore, look for unusual activity on your network. This can include file permission changes, the running of unexpected processes, or outbound connections related to malicious activity.
Step 3: Investigate Other Information Sources.
Finally, investigate other information sources like DNS records, WHOIS records, and other online sources that may give you additional information about where and how a malicious email was sent from. It is also important to look at your security cameras. They may have recorded footage of someone accessing your network or building.
Conclusion about Business Email Compromise Scams
BEC scams are a sophisticated type of cyberattack that targets businesses of all sizes. Organizations need to be vigilant against these types of attacks and know the signs of a BEC scam to recognize them.
Organizations can protect themselves by closely monitoring emails, researching potential targets, and being aware of suspicious URLs and exact-match domains. Additionally, businesses should report any instance of BEC scams to the FBI’s IC3, or your respective country and contact their financial institution immediately.
EXPECTATION MANAGEMENT RE IC3 REPORTING: Less than one in ten thousand cybercrimes are prosecuted in the USA and other western countries, so don’t get your hopes up for justice. If you have suffered significant losses and can justify the expense of hiring a digital private investigator to value add or even solve your case for the Dept. of Justice, then the chances of justice and recovery are greatly enhanced. This is why Rexxfield recruits retired DOJ Special Agents to find the best venues for our clients’ cases.