What is BEC? -Business Email Compromise Definition
What is a Business Email Compromise Attack?
Business email compromise (BEC), also known as email account compromise (EAC), is a form of cybercrime where scammers use legitimate email accounts and/or spoofed email accounts to trick their victims into sending money or disclosing confidential company information. BEC scammers most often accomplish this by carefully applying social engineering techniques as they impersonate vendors, executives and decision-makers. Then, they will send fraudulent instructions to the target requesting payment via wire transfer, PayPal invoice, or some other means.
The most common types of BEC attacks are vendor email compromise and CEO Fraud, such email accounts represent individuals with considerable authority in authorising business transactions and the transfer of funds, because of this and the widespread nature of Business Email Compromise scams, BEC is one of the most financially damaging cybercrimes.
BEC attacks target the weakest link in most modern business financial/organisational systems: the people within it. BEC attacks rely on the familiarity of the target with whoever they are impersonating. This means BEC attackers can easily source sensitive data.
The emails used in a BEC scam are created to appear to be coming from a known source with a legitimate request. Like these examples of business email compromise from the FBI website:
- A vendor your business regularly deals with emails an invoice with an updated mailing address.
- A company CEO asks her assistant to buy gift cards to give employees as rewards. The CEO asks for the serial numbers, so he can email them out to everyone.
- A homebuyer is sent an email from his title company with instructions on how to wire the down payment.
These and many more similar scenarios happened and still happen, to real victims all over the world. And in most cases, thousands, or even hundreds of thousands of dollars, were transferred to the scammers instead.
Common Types of Business Email Compromise Scams
BEC scams come in many forms, but they are all similar in how they work. These are standard practices within BEC scams:
Email accounts compromise impersonation or website.
The scammers use sight variations on legitimate addresses. For example, is turned into . This small variation fools victims into thinking fake accounts are authentic. This type of attack can therefore easily allow attackers to send fraudulent emails that appear to have come from executives, or other individuals with the authority to approve the request within the BEC email.
Spear Phishing emails.
These emails are a type of phishing attack created to appear as if they come from a trusted sender to trick victims into sharing confidential information. They seek information that gives them access to company accounts, calendars, and data to gather the details they need to carry out the BEC schemes.
Malware
BEC scam emails contain malicious software to infiltrate company networks and gain access to legitimate emails about billing and invoices. They use that information to send invoices and payment reminders at the right time, so accountants or financial officers don’t question payment requests. Malware also gives criminals undetected access to a victim’s data, such as passwords and financial account information.
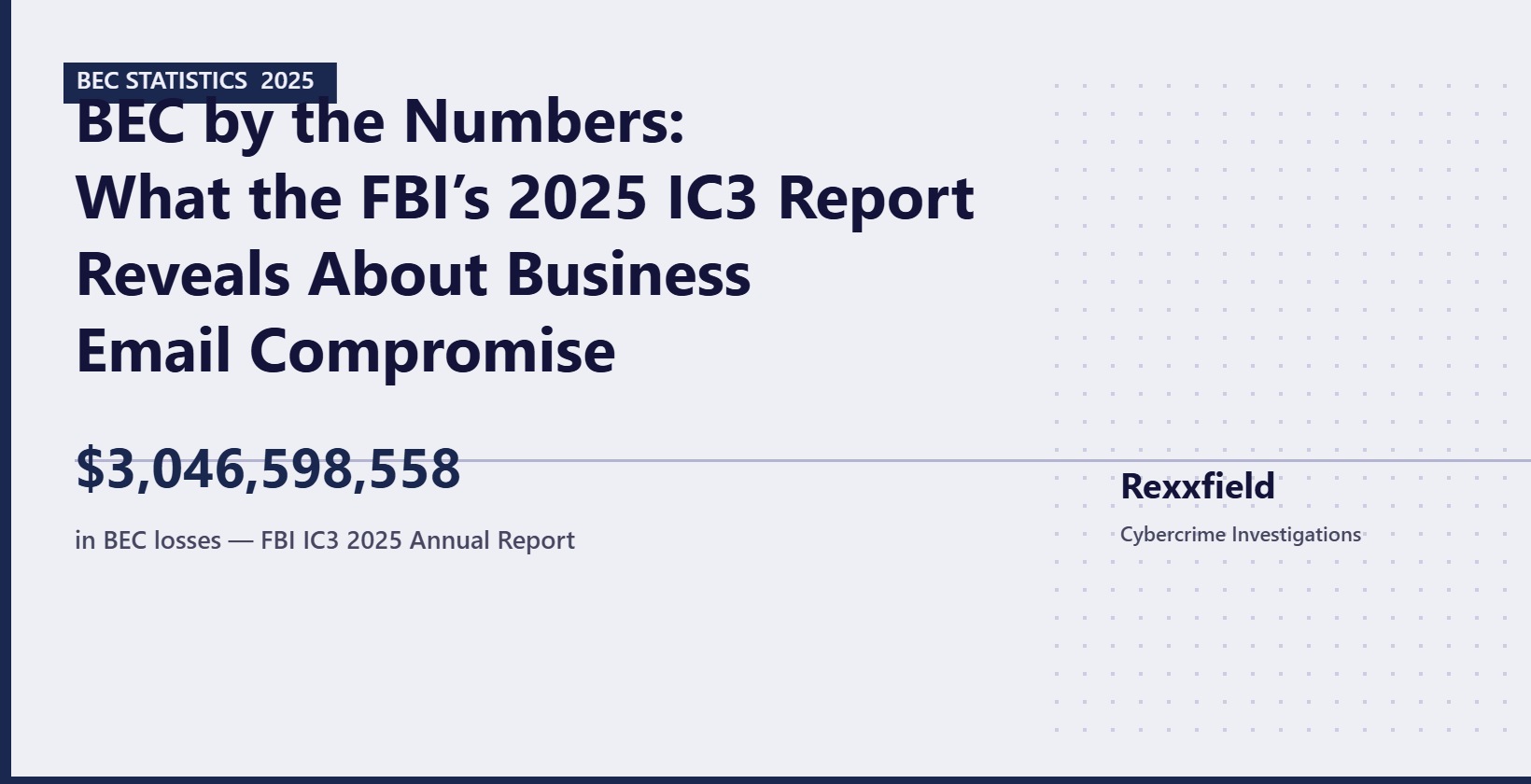
The Losses of Business Email Compromise (BEC)
Business Email Compromise or BEC is a form of phishing attack. Phishing attacks are still one of the most prevalent forms of cybercrime targeting businesses and organizations today. But the Business Email Compromise has been especially lucrative for cybercriminals. According to the FBI’s Internet Crime Complaint Center (IC3), BEC attacks resulted in over $43 billion in losses between June 2016 and December 2021.
With tech evolving, and as businesses move to adjust to working from home, and remote collaboration, these losses are only expected to grow, with BEC attacks increasing in frequency and sophistication.
Preventing Business Email Compromise
The rise of the Business Email Compromise (STATISTIC) and the desire to protect against them, is quickly making email security a crucial element of any onboarding process. Secure email gateways and advanced email security solutions are crucial in safeguarding against these threats. They work by scrutinizing incoming emails, and filtering out those with spoofed email addresses or suspicious content indicative of a potential BEC attack. Employee awareness is also key; training them to recognize the hallmarks of BEC, such as changes in payment details or requests from what appears to be an employee’s email account but is actually hacked, can significantly reduce the risk. The goal of a BEC is often to manipulate business transactions via email; hence, verifying any unusual requests directly through known contacts is a practice that can stop BEC attacks in their tracks.
How To Protect Against BEC Scams with Email Security
To further protect against BEC, it’s essential to implement stringent email protection policies. Regularly analyse email content for red flags and use security software to monitor for signs of hacked employee email accounts. Email security solutions should be a part of a larger strategy to prevent BEC, which also involves keeping private information secure and limiting access to a legitimate email account to authorized personnel only. BEC attacks can target any employee. To prevent these attacks, it is important to have a culture of vigilance and continuously educate employees about the latest BEC tactics.
Recognizing BEC Attacks
As described above, there are multiple ways scammers convince their victims that their email is genuine. This includes email spoofing, email impersonation, and email account takeover. If you and your employees can identify these tactics, you can protect your business against business email compromises. There are a few concepts to be aware of when working to analyse emails and detect BEC and EAC attacks.
Email impersonation:
Email impersonation is a simple tactic where the scammer uses an email account that looks very similar to a real business email account. The email address or display name looks nearly identical to the actual sender’s account, but you can recognize these altered accounts and their suspicious emails. They use spelling tricks or special characters to make the email address look similar.
For example, vs . Or a change in the company name, like the example from Varonis below.
Email Impersonation is a commonly used and simple strategy where the attacker will set up an email account that looks very similar to an actual business email account. The attacker’s email address or display name will look almost identical to the actual sender. However, it may utilize spelling tricks or special characters from different languages to make the email look convincing.
Email spoofing:
Email spoofing is when scammers forge the domain of their fake emails to represent the email domain of the targeted organization. By evading email authentication standards such as SPF, DKIM, and DMARC, attackers can spoof their emails to make them look like it’s coming from a legitimate domain instead of the scammer’s email server. Once it’s done, scamming the contacts of that legitimate email address can be as simple as editing a past invoice. The attackers insert the details of a fraudulent bank account and send them the customers/employees of their victim.
A misconfiguration of SPF and DMARC can allow attackers to spoof sender domains.
Email Account Takeover:
Email Account Takeover is a more advanced way of business email compromise where the criminal obtains access to a legitimate email account, most often someone’s corporate email account. The criminal can obtain credentials via phishing or using usernames/passwords exposed in previous breaches.
By having access to a compromised business email account, the criminal can analyse the account’s contacts, emails, and other information. The criminal will also, in most cases, create forwarding rules to their external email to gather information outside the victim.
The criminal will search for emails with sensitive information or financial transactions. Once something of interest is discovered, they embed themselves within an ongoing email treat or use email impersonation and spoofing to manipulate the trusting account holder to carry out a specific action, such as transferring money.
A common wire fraud tactic used with BEC scams is to steal a copy of a real invoice and change the banking and routing information.
Additionally, a compromised email account may show some of the following indicators in Microsoft Exchange:
- Unintended profile changes such as changes to the name and contact information
- Inbox rules that the email account holder did not create, like automatically forwarding emails to folders like Notes or RSS
- Other people receive emails from the compromised account without those emails being present in the Sent folder.
- The mailbox has been blocked from sending emails.
Business Email Compromise Investigation
Businesses that fell victim to a BEC scam, or believe that their email account is hacked, should report and submit a complaint form to the FBI’s IC3, and contact their financial institution immediately.
IC3 REPORTING EXPECTATION MANAGEMENT: In the USA, less than one in ten thousand cybercrimes are prosecuted, and other Western countries are not doing much better, so don’t get your hopes up for justice. If you have suffered significant losses and can justify the cost of engaging a cyber investigator to value add or even solve your case for the Department of Justice, the chance of justice and recovery greatly increase. This is why Rexxfield has retired DOJ Special Agents in its team to find the best venues for our client’s cases.